Music and Sound intercom systems also ensure peace of mind with enhanced security and room monitoring features. For more than 50 years, a company named M&S Systems has been the leading designer and manufacturer of fine systems for home communication and entertainment. Intercom—Adjusts the volume for the system intercom Tone Loudness Treble Bass Balance (if you have the optional stereo power amplifier) Function Recommended Setting from Software VER 1.7 and 1.9 Master Volume 10 Loudness On Treble 10 Bass 8 Balance (optional mc960PA only) 0 Intercom Volume 10 Function Recommended Setting from.
- M&S Intercom Systems and replacement intercom systems. We offer complete system kits, retrofit intercom kits to replace your M&S system, components for new systems. Whether you need a new intercom, want to replace your old system or need replacement an M&S intercom, we have the products you need.
- Free Intercom Design & Price Quote. If you are looking for personalized assistance to upgrade your current home intercom or to install a new system, then look no further than Home Controls. One of our dedicated intercom experts can create a custom solution, complete with a parts list and prices. » Request your personalized home intercom quote.
- Music and Sound intercom systems also ensure peace of mind with enhanced security and room monitoring features. For more than 50 years, a company named M&S Systems has been the leading designer and manufacturer of fine systems for home communication and entertainment.
Vulnerability in Group Policy Could Allow Remote Code Execution (3000483)
Published: February 10, 2015 | Updated: March 11, 2015
Version: 1.1
Ms Intercom Systems For Home
Executive Summary
This security update resolves a privately reported vulnerability in Microsoft Windows. The vulnerability could allow remote code execution if an attacker convinces a user with a domain-configured system to connect to an attacker-controlled network. An attacker who successfully exploited this vulnerability could take complete control of an affected system. Best apps for macbook air 2019. An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights.
This security update is rated Critical for all supported editions of Windows Server 2003, Windows Vista, Windows Server 2008, Windows 7, Windows Server 2008 R2, Windows 8, Windows Server 2012, Windows RT, Windows 8.1, Windows Server 2012 R2, and Windows RT 8.1. For more information, see the Affected Software section.
The security update addresses the vulnerability by improving how domain-configured systems connect to domain controllers prior to Group Policy accepting configuration data. Cyber bingo review. For more information about the vulnerability, see the Vulnerability Information section.
To be protected from the vulnerability described in this bulletin, additional configuration by a system administrator is required in addition to deploying this security update. For more information about this update, see Microsoft Knowledge Base Article 3000483.
Affected Software
The following software versions or editions are affected. Versions or editions that are not listed are either past their support life cycle or are not affected. To determine the support life cycle for your software version or edition, see Microsoft Support Lifecycle.
| **Operating System** | **Maximum Security Impact** | **Aggregate Severity Rating** | **Updates Replaced** |
| **Windows Server 2003** | |||
| Windows Server 2003 Service Pack 2[1] | Remote Code Execution | Critical | None |
| Windows Server 2003 x64 Edition Service Pack 2[1] | Remote Code Execution | Critical | None |
| Windows Server 2003 with SP2 for Itanium-based Systems[1] | Remote Code Execution | Critical | None |
| **Windows Vista** | |||
| [Windows Vista Service Pack 2](https://www.microsoft.com/download/details.aspx?familyid=ddf6f5df-113d-4e08-9422-d72f1bb3ea01) (3000483) | Remote Code Execution | Critical | 2536276 in [MS11-043](http://go.microsoft.com/fwlink/?linkid=215841) and 2839229 in [MS13-048](http://go.microsoft.com/fwlink/?linkid=301748) |
| [Windows Vista x64 Edition Service Pack 2](https://www.microsoft.com/download/details.aspx?familyid=ab8a7a65-a0f6-4f79-99ed-4b4cfcbcadfd) (3000483) | Remote Code Execution | Critical | 2536276 in [MS11-043](http://go.microsoft.com/fwlink/?linkid=215841) and 2813170 in [MS13-031](http://go.microsoft.com/fwlink/?linkid=282388) |
| **Windows Server 2008** | |||
| [Windows Server 2008 for 32-bit Systems Service Pack 2](https://www.microsoft.com/download/details.aspx?familyid=a507236d-0ce1-4e8c-adbe-20186f2c1e1b) (3000483) | Remote Code Execution | Critical | 2536276 in [MS11-043](http://go.microsoft.com/fwlink/?linkid=215841) and 2839229 in [MS13-048](http://go.microsoft.com/fwlink/?linkid=301748) |
| [Windows Server 2008 for x64-based Systems Service Pack 2](https://www.microsoft.com/download/details.aspx?familyid=5b009bb4-738d-42ce-9e35-5d4580b0ad25) (3000483) | Remote Code Execution | Critical | 2536276 in [MS11-043](http://go.microsoft.com/fwlink/?linkid=215841) and 2813170 in [MS13-031](http://go.microsoft.com/fwlink/?linkid=282388) |
| [Windows Server 2008 for Itanium-based Systems Service Pack 2](https://www.microsoft.com/download/details.aspx?familyid=7c37a025-81ea-4360-bcde-65b39171202f) (3000483) | Remote Code Execution | Critical | 2536276 in [MS11-043](http://go.microsoft.com/fwlink/?linkid=215841) and 2813170 in [MS13-031](http://go.microsoft.com/fwlink/?linkid=282388) |
| **Windows 7** | |||
| [Windows 7 for 32-bit Systems Service Pack 1](https://www.microsoft.com/download/details.aspx?familyid=51090490-014f-41c4-a9e5-00765457737f) (3000483) | Remote Code Execution | Critical | 2536276 in [MS11-043](http://go.microsoft.com/fwlink/?linkid=215841) and 3023266 in [MS15-001](http://go.microsoft.com/fwlink/?linkid=522536) |
| [Windows 7 for x64-based Systems Service Pack 1](https://www.microsoft.com/download/details.aspx?familyid=0f56004d-5870-4294-b630-2f984640e8c6) (3000483) | Remote Code Execution | Critical | 2536276 in [MS11-043](http://go.microsoft.com/fwlink/?linkid=215841) and 3023266 in [MS15-001](http://go.microsoft.com/fwlink/?linkid=522536) |
| **Windows Server 2008 R2** | |||
| [Windows Server 2008 R2 for x64-based Systems Service Pack 1](https://www.microsoft.com/download/details.aspx?familyid=b52b259b-5c72-46a9-8559-3d38c0c7a126) (3000483) | Remote Code Execution | Critical | 2536276 in [MS11-043](http://go.microsoft.com/fwlink/?linkid=215841) and 3023266 in [MS15-001](http://go.microsoft.com/fwlink/?linkid=522536) |
| [Windows Server 2008 R2 for Itanium-based Systems Service Pack 1](https://www.microsoft.com/download/details.aspx?familyid=432b66df-a531-4280-9aaf-6ce696e2f696) (3000483) | Remote Code Execution | Critical | 2536276 in [MS11-043](http://go.microsoft.com/fwlink/?linkid=215841) and 3023266 in [MS15-001](http://go.microsoft.com/fwlink/?linkid=522536) |
| **Windows 8 and Windows 8.1** | |||
| [Windows 8 for 32-bit Systems](https://www.microsoft.com/download/details.aspx?familyid=54e7605b-a6b3-445f-9d43-ac3fa937bc47) (3000483) | Remote Code Execution | Critical | 3023266 in [MS15-001](http://go.microsoft.com/fwlink/?linkid=522536) |
| [Windows 8 for x64-based Systems](https://www.microsoft.com/download/details.aspx?familyid=374c14fc-82cf-4cfa-94f0-695e99d7c423) (3000483) | Remote Code Execution | Critical | 3023266 in [MS15-001](http://go.microsoft.com/fwlink/?linkid=522536) |
| [Windows 8.1 for 32-bit Systems](https://www.microsoft.com/download/details.aspx?familyid=29857dc6-8dec-41c1-afee-a898d602d3ef) (3000483) | Remote Code Execution | Critical | None |
| [Windows 8.1 for x64-based Systems](https://www.microsoft.com/download/details.aspx?familyid=f0adfdbe-6056-4be1-8294-3b808c0a0e89) (3000483) | Remote Code Execution | Critical | None |
| **Windows Server 2012 and Windows Server 2012 R2** | |||
| [Windows Server 2012](https://www.microsoft.com/download/details.aspx?familyid=1e6052c8-77a2-4bfd-905f-50e86d6e5efa) (3000483) | Remote Code Execution | Critical | 3023266 in [MS15-001](http://go.microsoft.com/fwlink/?linkid=522536) |
| [Windows Server 2012 R2](https://www.microsoft.com/download/details.aspx?familyid=48248922-d55a-43b7-a564-671d79127ac7) (3000483) | Remote Code Execution | Critical | None |
| **Windows RT and Windows RT 8.1** | |||
| Windows RT[2](3000483) | Remote Code Execution | Critical | 3023266 in [MS15-001](http://go.microsoft.com/fwlink/?linkid=522536) |
| Windows RT 8.1[2](3000483) | Remote Code Execution | Critical | None |
| **Server Core installation option** | |||
| [Windows Server 2008 for 32-bit Systems Service Pack 2](https://www.microsoft.com/download/details.aspx?familyid=a507236d-0ce1-4e8c-adbe-20186f2c1e1b) (Server Core installation) (3000483) | Remote Code Execution | Critical | 2536276 in [MS11-043](http://go.microsoft.com/fwlink/?linkid=215841) and 2839229 in [MS13-048](http://go.microsoft.com/fwlink/?linkid=301748) |
| [Windows Server 2008 for x64-based Systems Service Pack 2](https://www.microsoft.com/download/details.aspx?familyid=5b009bb4-738d-42ce-9e35-5d4580b0ad25) (Server Core installation) (3000483) | Remote Code Execution | Critical | 2536276 in [MS11-043](http://go.microsoft.com/fwlink/?linkid=215841) and 2813170 in [MS13-031](http://go.microsoft.com/fwlink/?linkid=282388) |
| [Windows Server 2008 R2 for x64-based Systems Service Pack 1](https://www.microsoft.com/download/details.aspx?familyid=b52b259b-5c72-46a9-8559-3d38c0c7a126) (Server Core installation) (3000483) | Remote Code Execution | Critical | 2536276 in [MS11-043](http://go.microsoft.com/fwlink/?linkid=215841) and 3023266 in [MS15-001](http://go.microsoft.com/fwlink/?linkid=522536) |
| [Windows Server 2012](https://www.microsoft.com/download/details.aspx?familyid=1e6052c8-77a2-4bfd-905f-50e86d6e5efa) (Server Core installation) (3000483) | Remote Code Execution | Critical | 3023266 in [MS15-001](http://go.microsoft.com/fwlink/?linkid=522536) |
| [Windows Server 2012 R2](https://www.microsoft.com/download/details.aspx?familyid=48248922-d55a-43b7-a564-671d79127ac7) (Server Core installation) (3000483) | Remote Code Execution | Critical | None |
[2]This update is available via Windows Update only.
Update FAQ
Does this update install any additional functionality?
Yes. For customers with automatic updating enabled, this update also installs new functionality that is being deployed with Microsoft Security Advisory 3004375. The new functionality, which pertains to the Windows Command Line Audit Process Creation policy, is unrelated to the vulnerabilities addressed in this bulletin. When installation is complete, updates 3000483 and 3004375 will be listed as installed updates. Youtube downloader for mac os x 10.5 8.
Important Customers who download and install updates manually will need to install both updates (3000483 and 3004375), which can be installed in any order.
Windows Server 2003 is listed as an affected product; why is Microsoft not issuing an update for it? Although Windows Server 2003 is an affected product, Microsoft is not issuing an update for it because the comprehensive architectural changes required would jeopardize system stability and cause application compatibility problems. Microsoft recommends that security-conscious customers upgrade to a later operating system in order to keep pace with the changing security threat landscape and benefit from the more robust protections that later operating systems provide.
Severity Ratings and Vulnerability Identifiers
The following severity ratings assume the potential maximum impact of the vulnerability. For information regarding the likelihood, within 30 days of this security bulletin's release, of the exploitability of the vulnerability in relation to its severity rating and security impact, please see the Exploitability Index in the February bulletin summary. https://belglosuare1986.mystrikingly.com/blog/detecting-spyware-on-macbook-pro.
| **Vulnerability Severity Rating and Maximum Security Impact by Affected Software** | ||
| **Affected Software** | [**Group Policy Remote Code Execution Vulnerability - CVE-2015-0008**](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2015-0008) | **Aggregate Severity Rating** |
| **Windows Server 2003** | ||
| Windows Server 2003 Service Pack 2 | **Critical** Remote Code Execution | **Critical** |
| Windows Server 2003 x64 Edition Service Pack 2 | **Critical** Remote Code Execution | **Critical** |
| Windows Server 2003 with SP2 for Itanium-based Systems | **Critical** Remote Code Execution | **Critical** |
| **Windows Vista** | ||
| Windows Vista Service Pack 2 (3000483) | **Critical** Remote Code Execution | **Critical** |
| Windows Vista x64 Edition Service Pack 2 (3000483) | **Critical** Remote Code Execution | **Critical** |
| **Windows Server 2008** | ||
| Windows Server 2008 for 32-bit Systems Service Pack 2 (3000483) | **Critical** Remote Code Execution | **Critical** |
| Windows Server 2008 for x64-based Systems Service Pack 2 (3000483) | **Critical** Remote Code Execution | **Critical** |
| Windows Server 2008 for Itanium-based Systems Service Pack 2 (3000483) | **Critical** Remote Code Execution | **Critical** |
| **Windows 7** | ||
| Windows 7 for 32-bit Systems Service Pack 1 (3000483) | **Critical** Remote Code Execution | **Critical** |
| Windows 7 for x64-based Systems Service Pack 1 (3000483) | **Critical** Remote Code Execution | **Critical** |
| **Windows Server 2008 R2** | ||
| Windows Server 2008 R2 for x64-based Systems Service Pack 1 (3000483) | **Critical** Remote Code Execution | **Critical** |
| Windows Server 2008 R2 for Itanium-based Systems Service Pack 1 (3000483) | **Critical** Remote Code Execution | **Critical** |
| **Windows 8 and Windows 8.1** | ||
| Windows 8 for 32-bit Systems (3000483) | **Critical** Remote Code Execution | **Critical** |
| Windows 8 for x64-based Systems (3000483) | **Critical** Remote Code Execution | **Critical** |
| Windows 8.1 for 32-bit Systems (3000483) | **Critical** Remote Code Execution | **Critical** |
| Windows 8.1 for x64-based Systems (3000483) | **Critical** Remote Code Execution | **Critical** |
| **Windows Server 2012 and Windows Server 2012 R2** | ||
| Windows Server 2012 (3000483) | **Critical** Remote Code Execution | **Critical** |
| Windows Server 2012 R2 (3000483) | **Critical** Remote Code Execution | **Critical** |
| **Windows RT and Windows RT 8.1** | ||
| Windows RT (3000483) | **Critical** Remote Code Execution | **Critical** |
| Windows RT 8.1 (3000483) | **Critical** Remote Code Execution | **Critical** |
| **Server Core installation option** | ||
| Windows Server 2008 for 32-bit Systems Service Pack 2 (Server Core installation) (3000483) | **Critical** Remote Code Execution | **Critical** |
| Windows Server 2008 for x64-based Systems Service Pack 2 (Server Core installation) (3000483) | **Critical** Remote Code Execution | **Critical** |
| Windows Server 2008 R2 for x64-based Systems Service Pack 1 (Server Core installation) (3000483) | **Critical** Remote Code Execution | **Critical** |
| Windows Server 2012 (Server Core installation) (3000483) | **Critical** Remote Code Execution | **Critical** |
| Windows Server 2012 R2 (Server Core installation) (3000483) | **Critical** Remote Code Execution | **Critical** |
Vulnerability Information
Group Policy Remote Code Execution Vulnerability - CVE-2015-0008
A remote code execution vulnerability exists in how Group Policy receives and applies policy data when a domain-joined system connects to a domain controller. To exploit this vulnerability, an attacker would have to convince a victim with a domain-configured system to connect to an attacker-controlled network.
An attacker who successfully exploited this vulnerability could take complete control of an affected system and then install programs; view, change, or delete data; or create new accounts with full user rights. The security update addresses the vulnerability by improving how domain-configured systems connect to domain controllers prior to Group Policy accepting configuration data.
This vulnerability has not been publicly disclosed. When this security bulletin was issued, Microsoft had not received any information to indicate that this vulnerability had been publicly used to attack customers.
Mitigating Factors
Microsoft has not identified any mitigating factors for this vulnerability.
Workarounds
Microsoft has not identified any workarounds for this vulnerability.
Security Update Deployment
For Security Update Deployment information, see the Microsoft Knowledge Base article referenced in the Executive Summary.
Acknowledgments
Microsoft recognizes the efforts of those in the security community who help us protect customers through coordinated vulnerability disclosure. See Acknowledgments for more information.
Disclaimer
The information provided in the Microsoft Knowledge Base is provided 'as is' without warranty of any kind. Microsoft disclaims all warranties, either express or implied, including the warranties of merchantability and fitness for a particular purpose. In no event shall Microsoft Corporation or its suppliers be liable for any damages whatsoever including direct, indirect, incidental, consequential, loss of business profits or special damages, even if Microsoft Corporation or its suppliers have been advised of the possibility of such damages. Some states do not allow the exclusion or limitation of liability for consequential or incidental damages so the foregoing limitation may not apply.

Microsoft has not identified any mitigating factors for this vulnerability.
Workarounds
Microsoft has not identified any workarounds for this vulnerability.
Security Update Deployment
For Security Update Deployment information, see the Microsoft Knowledge Base article referenced in the Executive Summary.
Acknowledgments
Microsoft recognizes the efforts of those in the security community who help us protect customers through coordinated vulnerability disclosure. See Acknowledgments for more information.
Disclaimer
The information provided in the Microsoft Knowledge Base is provided 'as is' without warranty of any kind. Microsoft disclaims all warranties, either express or implied, including the warranties of merchantability and fitness for a particular purpose. In no event shall Microsoft Corporation or its suppliers be liable for any damages whatsoever including direct, indirect, incidental, consequential, loss of business profits or special damages, even if Microsoft Corporation or its suppliers have been advised of the possibility of such damages. Some states do not allow the exclusion or limitation of liability for consequential or incidental damages so the foregoing limitation may not apply.
Revisions
- V1.0 (February 10, 2015): Bulletin published.
- V1.1 (March 11, 2015): Bulletin revised to correct the updates replaced for all supported editions of Windows Vista, Windows Server 2008, Windows 7, and Windows Server 2008 R2. This is an informational change only. There were no changes to the update files. Customers who have already successfully updated their systems do not need to take any action.
Page generated 2015-03-20 14:36Z-07:00.
Full-Function Intercom & Music Distribution System
The M&S DMC3-4 Music/Communication Retrofit System Master is a full-function intercom and music distribution system designed for retrofit applications in residential use. This M&S home intercom system can replace older intercom systems that use three-wire or four-wire connections to the room stations. The M&S DMC3-4 supports up to 15 room stations and up to three door speakers. The built-in AM/FM radio tuner allows setting eight AM station presets and eight FM station presets. The M&S home intercom system's back-lit liquid crystal display shows the operation mode, audio source, radio frequency, volume setting, and time. With the optional Model dmc1 Bluetooth Player installed, you can stream audio from any Bluetooth enabled device through your music and intercom system, as well as connect any device that uses a 3.5mm plug, such as a MP3 or CD player.
Room stations have push-buttons that control the system operation. Retrofit room and patio stations connect to the M&S home intercom system using the installation's existing wiring. All room station models can select talk or listen to other room stations, door speakers and the master unit. Each M&S DMC3-4 room station has an intercom volume control. The dmc3RS or dmc4rs room stations and dmc3RW or dmc4RW patio stations can select the audio source, control the radio tuner, and set the master music volume.
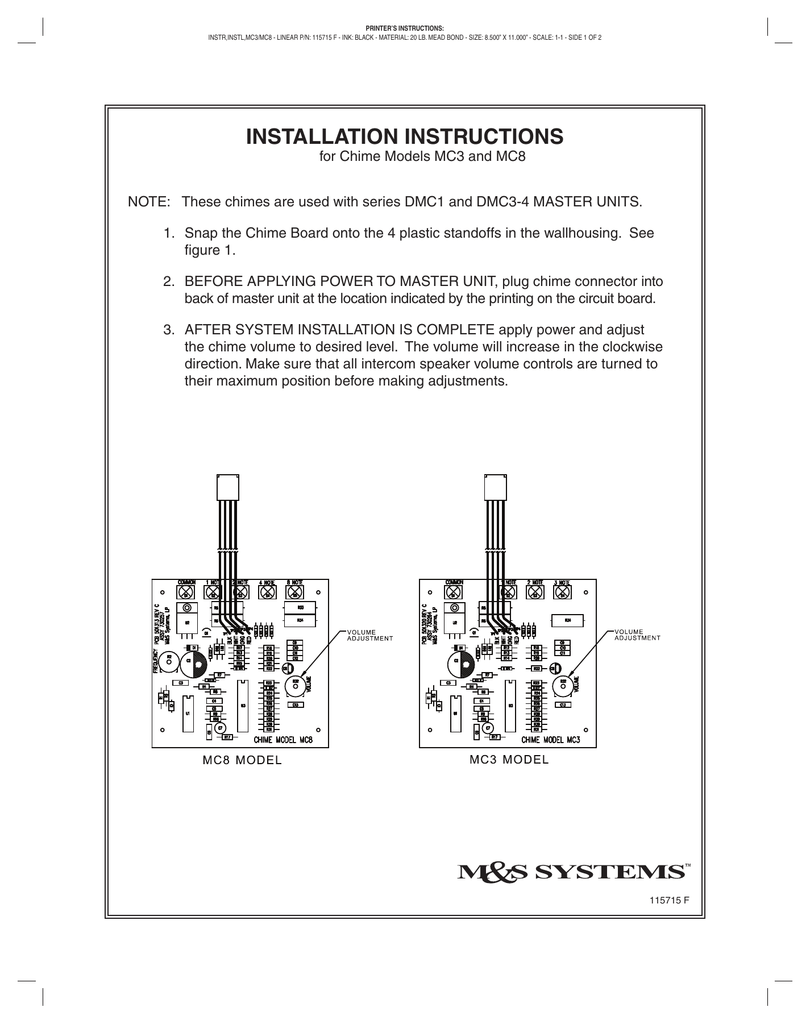
For access control, the optional Model DRW Door Release Mechanism can be installed and activated from the master unit or room stations. The optional three-note Model MC3 or eight-note Model MC8 chime modules provide a selection of door chime sounds.
For master unit rough in and finish-out components order the Model dmc1H Wall Housing Kit to mount the dmc3-4 master. If the optional Model dmc1 Bluetooth Player is used, order the dmc1HC Wall Housing Kit. For the retrofit frames, follow this guide:
- When replacing a master only system with a dmc3-4 master use a Model dmcFM Master Retrofit Mounting Frame.
- When replacing a combination system with a dmc3-4 use a Model dmcFC Combination Retrofit Mounting Frame.
- When replacing a master only system with a dmc3-4 and dmc1 Bluetooth Player use a Model dmc1F Combination Mounting Frame. Note: This type of retrofit will require the hole in the wall to be made larger.
- For all retrofit indoor room stations use a Model dmcFR Room Station Retrofit Mounting Frame (available in White, almond, and black).
- For all outdoor or high sun area flush-mount retrofit patio stations use a Model dmcFRW Patio Station Retrofit Mounting Frame.
- For all outdoor surface-mount patio stations use a Model dmc1HRWS Surface-mount Rough-in Enclosure.
- For NuTone door speaker replacements use Model dmcFD Door Speaker Retrofit Mounting Frame (not required when replacing old style M&S door speakers).
Getting started with mplus version 8.1 for mac. NOTE: All room stations, patio stations, and door speakers must be replaced when installing an M&S DMC3-4 retrofit system.
M&S Systems Integrated Home Technologies
For more than 50 years, M&S Systems has been the leading designer and manufacturer of fine systems for home communication and entertainment. These M&S home intercom systems revolutionized home communications with technology, style and value. That company is now part of Linear, where the legacy of quality in design and development continues on.
Product Features
- White faceplate color
- Retrofit for 3 and 4-wire intercom systems
- Supports up to 15 room stations
- Supports up to 3 door speakers
- 30 Watts (RMS) maximum output power
- Two music source inputs
- Eight AM and eight FM radio station tuner presets
- Stereo upgrade with optional power amplifier
- Remote volume and source control from room stations
- Intercom only and door release features
- Programmable monitor override
- Automatic on/off feature
- Optional three-note and eight-note door chime
Technical Details
- Manufacturer Part #:
- DMC3-4: White
- DMC3-4A: Almond
- DMC3-4B: Black
- Warranty: 2 Years
»M&S DMC3-4 Music & Intercom System Installation Manual (.pdf)
You may also like
Ms Intercom Systems Install Manual 2016
- M&S DMC Intercom Room Station, 3-Wire Retrofit
- M&S DMC Music & Intercom Master Station Mounting Frame, Retrofit
- M&S DMC Intercom Patio Station, Remote Scan, Master Volume, 4-Wire Retrofit
- M&S DMC Intercom Patio Station, Remote Scan, Master Volume, 3-Wire Retrofit
